 I’ve just installed the Dovecot Mail Service on one of my Plesk 12 servers. It’s an alternative to the old favourite Courier IMAP/POP and a new addition in Plesk 12.
I’ve just installed the Dovecot Mail Service on one of my Plesk 12 servers. It’s an alternative to the old favourite Courier IMAP/POP and a new addition in Plesk 12.
Dovecot does more or less the same as Courier (i.e. lets you receive mail), but it’s a bit more configurable and debug friendly. It also offers server-side mail filtering which is accessible via the Plesk Webmail services Roundcube and Horde.
In this article I’ll show you how to install Dovecot in Plesk 12, and how to add your own SSL certificates for mail. In my previous article I’ve explained how to do this with the standard Courier Mail service.
Installing Dovecot in Plesk 12
Head over to
- Tools and Settings (or the Server Tab)
- under the Plesk heading
- Updates and Upgrades
Select Add or Remove Components and under Mail Hosting Features, find the option for Different IMAP/POP3 server:
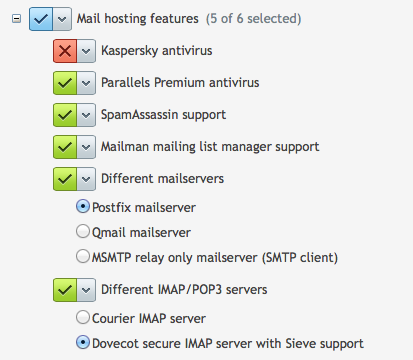
You can only install either Courier or Dovecot. Switching will automatically uninstall the component you currently have and instead install the other one.
Note that switching Courier for Dovecot will preserve all mailboxes and will not affect your outgoing mail services. Give Plesk a moment until your see the “installation has finished” message.
You’re now running Dovecot!
Patching Dovecot SSL Certificates
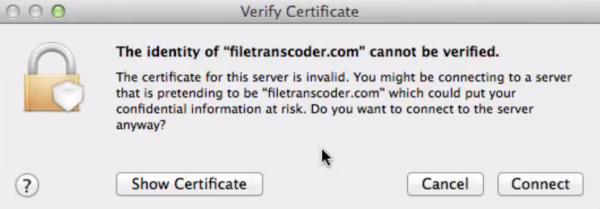
As with Courier, Dovecot will use self-signed certificates for secure connections. This means that a nasty window is likely to pop up when clients connect. You can suppress this window by specifying your own SSL Certificates.
The default configuration file for Dovecot is in /etc/dovecot/dovecot.conf. However the file states that any changes you make here are wiped when an upgrade comes along. Instead, take a look at the /etc/dovecot/conf.d/ directory in which you’ll find three files by default:
- 10-plesk-security.conf
- 15-plesk-auth.conf
- 90-plesk-sieve.conf
You can add your own configuration snippets here, each beginning with a number and ending with .conf. The lower the number, the earlier your snippet is loaded. The higher the number, the later it is loaded. You get the picture.
Let’s create /etc/dovecot/conf.d/5-ssl.conf for our purposes. Because I had already configured my certificates for Courier they are still in /usr/share/imapd.pem – but feel free to place your .pem files anywhere you like. Here’s what my file looks like:
# SSL Certificates for Dovecot are defined here ssl = yes # Path to your Certificate, preferred permissions: root:root 0444 ssl_cert =Dovecot lets you have separate files for the certificate and the private key, something that's not possible in Courier as far as I know. Dovecot is also happy to keep those in the same file though as in my example, and as in Courier. Easy going I say!
For the changes to take effect we need to restart the Plesk Mail Service like so:
/usr/local/psa/admin/sbin/mailmng --restart-serviceThat's it!
How do I add a certificate for outgoing mail?
Postfix (and QMail) deal with sending mail, Dovecot and Courier only deal with receiving it. I've described how to add SSL Certificates to Postfix in my article about Courer.
Further Reading
- Nikolay explains how to use server-side filtering with Horde and Roundcube on the Plesk Dev Blog
- More details on Dovecot SSL Configuration
- Official Dovecot Documentation
- Wikipedia on Dovecot
- Check your new mail server with this handy online tool

I’ve had a good bit of trouble getting it to work and testing it correctly.
Here is my configuration
/etc/dovecot/conf.d/5-custom-ssl.conf
for debugging
verbose_ssl = yes
ssl = yes
Path to your Certificate, preferred permissions: root:root 0444
ssl_cert = </usr/local/etc/ssl/dovecot-cert.pem
Path to your Private Key, preferred permissions: root:root 0400
ssl_key = </usr/local/etc/ssl/dovecot-key.pem
Path to your CA file,
ssl_ca = </usr/local/etc/ssl/comodo-positiveSSL/AddTrustExternalCARoot.crt
ssl_ca = </usr/local/etc/ssl/comodo-positiveSSL/COMODORSAAddTrustCA.crt
ssl_ca = </usr/local/etc/ssl/comodo-positiveSSL/COMODORSADomainValidationSecureServerCA.crt
ssl_verify_client_cert = yes
auth_ssl_require_client_cert = yes
#auth_ssl_username_from_cert = yes
#EOF
openssl s_client -CApath /etc/ssl/certs -CAfile /etc/ssl/certs/ca-bundle.crt -cert ./postfix-cert.pem -key ./postfix-key.pem -connect smtp.foobar.com:110 -starttls pop
openssl s_client -CApath /etc/ssl/certs -CAfile /etc/ssl/certs/ca-bundle.crt -cert ./postfix-cert.pem -key ./postfix-key.pem -connect smtp.foobar.com:143 -starttls imap
Post about Postfix & Dovecot, *(post is still under moderation)
https://talk.plesk.com/threads/postfix-dovecot-cert-error.334931/#post-808783
Hi there!
I noticed on your Further Reading section you mentioned “Check your new mail server with this handy online tool”.
We created a secure email checker with a little better UI that may give a better experience to your readers.
Here’s the link: https://www.paubox.com/secure-email-check
Let me know if you think it’s an improvement, thank you!
Cheers,
Arianna